Update 2015/08/04: Works on Fedora 22 too. I recently applied the exact same procedure with success.
A quick update from a previous post for setting Metasploit on Fedora 21, the latest version.
It is mainly a copy and paste, except for a few typo fixes and some changes on the Ruby part. The good news is that Metasploit was recently ported to Ruby 2.x, so we don’t need anymore the rvm stuff anymore, which makes the process much simpler.
Preparing Postgresql
Install:
yum -y install postgresql-server postgresql-devel
Initiate a new “cluster” and connect to the sql client through the postgres user:
# as root:
postgresql-setup initdb
systemctl start postgresql.service
su postgres
psql
Inside the psql console, create the new Metasploit user and its database:
create user msf;
alter user msf with encrypted password 'super password';
create database msfdb;
grant all privileges on database msfdb to msf;
\q
Then, we will tell to Postgres how to accept local connections. ident necessitates an system account, trust means no password for any local account and md5 stands for a classic password authentication, which we will prefer.
Back to a root terminal, add this line inside /var/lib/pgsql/data/pg_hba.conf and beware that the order is important:
# IPv4 local connections:
host msfdb msf 127.0.0.1/32 md5
host all all 127.0.0.1/32 ident
Then we can restart the service and check with psql that the credentials are working:
systemctl restart postgresql.service
psql -U msf msfdb -h localhost
\q
Setting Ruby
Metasploit runs well with Ruby 1.9.3, so we will install this version and switch to it using rbenv.
rbenv does a nice job at managing several version of ruby next to each other, installing dependancies (as OpenSSL) and setting PATH:
# as root:
yum install ruby rubygems ruby-devel rubygem-bundler
Getting and running Metasploit
Install:
# as root in e.g. /opt
git clone https://github.com/rapid7/metasploit-framework.git msf
cd msf
yum -y install libpcap-devel sqlite-devel
./msfupdate
The installation of ruby modules will take a while. Then, configure the database by creating config/database.yml:
production:
adapter: postgresql
database: msfdb
username: msf
password:
host: 127.0.0.1
port: 5432
pool: 75
timeout: 5
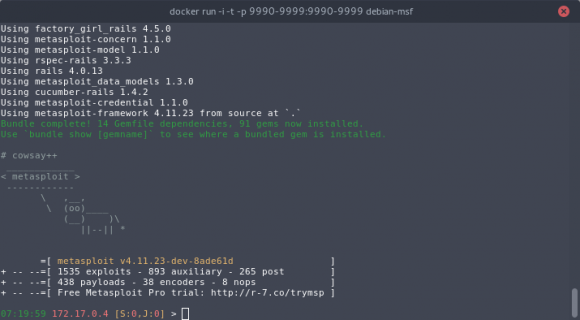
Launch it and have fun :
# as root
./msfconsole
# check connection to the database
db_status
You may want to add a cron entry in /etc/crontab to get regular updates (though it may break from time to time due to broken dependencies, so you are advised to check it sometimes):
# msfupdate every 2 hours
0 */2 * * * root /opt/msf/msfupdate 2>&1