Found on Full Disclosure, a weired but troubling connection of two security affairs : the OpenBSD backdoor rumor and the stuxnet worm.
Tag Archives: IPSEC
Perl : how to monitor a service remotely using sockets
I came to program my first Perl script based on sockets, after setting an IPSEC tunnel.
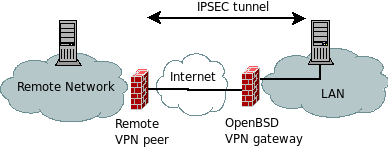
This tunnel is linking the remote peer and the local peer through an OpenBSD VPN gateway (managed with Isakmp).
The problem is that time allowed for this connection is limited, for security policy reasons. So it is not a 24- hour standard tunnel, but rather an on-demand type connection.
Note that the connection is automatically reset by the remote peer, by invalidating the connection cookie and therefore oblige to renegotiate the VPN tunnel from the beginning (phase 1 of the key exchange).
In other words, the Isakmp service has to be restarted every time we need the tunnel to be up.
Of course, it is not the purpose of Isakmp to have such a mechanism and what we want is to start the tunnel from the local peer, every time it needs to do some transfer.
The graph below summarizes the situation :
That is why I came to develop a script that opens a socket and allows the peer to remotely restart the Isakmp service.